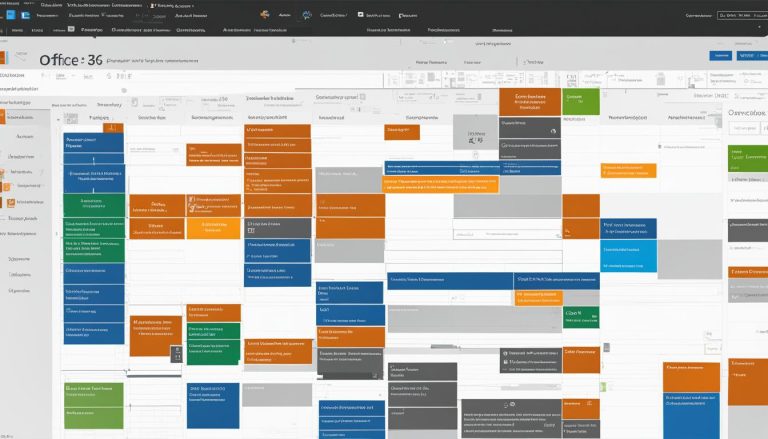
Understanding the Basics: What is Office 365?
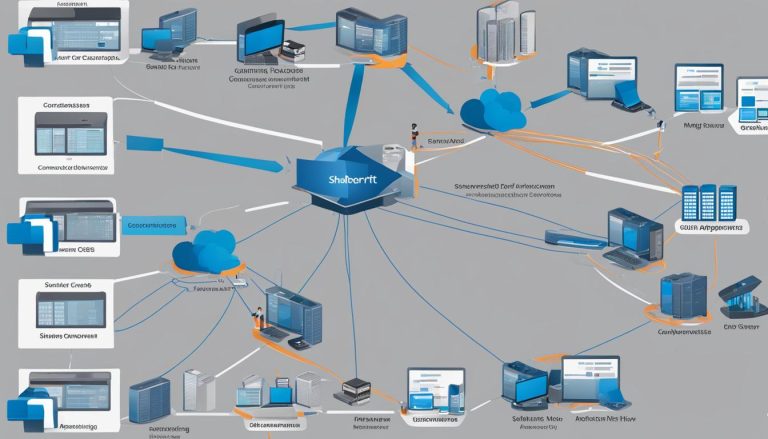
Office 365 is a cloud-based productivity suite that offers a range of features and benefits for individuals and businesses. It is a subscription model version of Microsoft’s popular productivity suite, Microsoft Office. With Office 365, users have access to core…