Learning how to perform an Ubuntu server setup 2026 is essential for anyone managing Linux infrastructure in the modern cloud era. Whether you’re deploying a web application, hosting a database, or building a microservices architecture, the initial configuration of your Ubuntu server determines your system’s security, stability, and performance. This comprehensive guide walks you through every step of Ubuntu server setup 2026, from installation to production-ready hardening, using the latest Ubuntu 24.04 LTS and 24.10 releases.
Why Ubuntu Server Setup 2026 Matters
A properly configured Ubuntu server setup 2026 protects your infrastructure from common attack vectors, prevents accidental lockouts, and establishes a solid foundation for deploying applications. In 2026, with the proliferation of cloud infrastructure, container orchestration, and remote work environments, server security is more critical than ever. A single misconfiguration during Ubuntu server setup 2026 can expose your entire network to threats.
This guide focuses on Ubuntu 24.04 LTS (Long Term Support), which receives five years of security updates and maintenance, making it the ideal choice for production servers. We’ll also cover compatibility with Ubuntu 24.10 and the upcoming 25.x releases.
Prerequisites for Ubuntu Server Setup 2026
Before starting your Ubuntu server setup 2026, ensure you have:
- Ubuntu Server installation media (USB drive or ISO for virtual machines)
- Physical or virtual machine with minimum 2GB RAM and 20GB storage
- Network connectivity for downloading updates and packages
- Root or sudo access to the system (we’ll configure this during setup)
- SSH client on your local machine (OpenSSH, PuTTY, or Terminal)
Step 1: Install Ubuntu Server
The first phase of Ubuntu server setup 2026 is the base installation. Follow these steps:
Installation Process
- Boot from installation media (USB drive or virtual ISO)
- Select language and keyboard layout
- Choose installation type: Select “Ubuntu Server” (minimal installation recommended for production)
- Configure network: Use DHCP for automatic IP assignment, or configure static IP for production servers
- Set hostname: Choose a descriptive name like
web-server-01ordb-prod-01 - Create admin user: Set a strong username (avoid “admin” or “root”) and complex password
- Enable OpenSSH server: Check the box to install SSH during setup (critical for remote access)
- Optional: Select featured snaps – Pre-install Docker, MicroK8s, PowerShell, or Nextcloud if needed
- Complete installation and reboot
After the first boot, log in with your created user credentials. This completes the basic Ubuntu server setup 2026 installation phase.
Step 2: Initial System Update
Immediately after logging in for the first time, update all system packages. This is a critical step in every Ubuntu server setup 2026 workflow:
sudo apt update
sudo apt upgrade -y
sudo apt dist-upgrade -y
sudo apt autoremove -y
This ensures your Ubuntu server setup 2026 includes the latest security patches and bug fixes. On Ubuntu 24.04 LTS, this process typically downloads 200-500MB of updates on a fresh installation.
Step 3: Create a Non-Root Sudo User
If you installed Ubuntu Server using root credentials or need additional administrative users, create a dedicated sudo user. This is a security best practice for Ubuntu server setup 2026:
# Log in as root (if applicable)
ssh root@your_server_ip
# Create new user
adduser deploy
# Add user to sudo group
usermod -aG sudo deploy
# Verify sudo access
su - deploy
sudo whoami # Should output: root
Never use the root account for daily operations. This Ubuntu server setup 2026 practice limits damage from accidental commands and provides better audit trails.
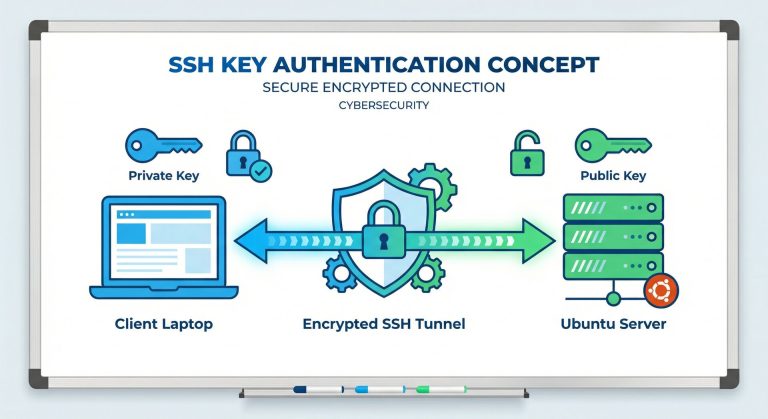
Step 4: Configure SSH for Secure Remote Access
SSH hardening is the most critical security step in Ubuntu server setup 2026. We’ll configure key-based authentication and disable password logins.
Generate SSH Keys (on your local machine)
# On your local computer (macOS, Linux, Windows WSL)
ssh-keygen -t ed25519 -C "your_email@example.com"
# Copy public key to server
ssh-copy-id -i ~/.ssh/id_ed25519.pub deploy@your_server_ip
# Test key authentication
ssh -i ~/.ssh/id_ed25519 deploy@your_server_ip
Harden SSH Configuration
Edit the SSH daemon configuration to disable password authentication and root login:
sudo nano /etc/ssh/sshd_config
Modify these settings for secure Ubuntu server setup 2026:
# Disable root login
PermitRootLogin no
# Disable password authentication (use keys only)
PasswordAuthentication no
PubkeyAuthentication yes
# Disable empty passwords
PermitEmptyPasswords no
# Change default SSH port (optional security through obscurity)
Port 2222
# Limit authentication attempts
MaxAuthTries 3
# Enable strict mode for key files
StrictModes yes
Save the file and restart SSH:
sudo systemctl restart ssh
Critical Warning: Before logging out, open a second SSH session to test your key authentication. This prevents lockouts during Ubuntu server setup 2026 SSH configuration.
Step 5: Enable and Configure UFW Firewall
Ubuntu’s Uncomplicated Firewall (UFW) provides simple yet powerful protection for your Ubuntu server setup 2026:
# Check UFW status (should be inactive on fresh install)
sudo ufw status
# Allow SSH before enabling firewall (prevent lockout!)
sudo ufw allow 22/tcp
# If you changed SSH port to 2222:
sudo ufw allow 2222/tcp
# Allow common services as needed
sudo ufw allow 80/tcp # HTTP
sudo ufw allow 443/tcp # HTTPS
# Enable firewall
sudo ufw enable
# Verify firewall rules
sudo ufw status verbose
Your output should show:
Status: active
To Action From
-- ------ ----
22/tcp ALLOW Anywhere
80/tcp ALLOW Anywhere
443/tcp ALLOW Anywhere
This firewall configuration is essential for production Ubuntu server setup 2026 security.
Step 6: Configure Automatic Security Updates
Enable unattended upgrades to automatically install security patches. This is crucial for maintaining secure Ubuntu server setup 2026 infrastructure:
sudo apt install unattended-upgrades -y
sudo dpkg-reconfigure -plow unattended-upgrades
Select “Yes” to enable automatic updates. Edit the configuration for fine-grained control:
sudo nano /etc/apt/apt.conf.d/50unattended-upgrades
Ensure these lines are uncommented:
"${distro_id}:${distro_codename}-security";
"${distro_id}ESMApps:${distro_codename}-apps-security";
Step 7: Set Up Fail2Ban for Intrusion Prevention
Fail2Ban monitors logs and bans IP addresses showing malicious behavior. This adds active defense to your Ubuntu server setup 2026:
sudo apt install fail2ban -y
# Create local configuration
sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
sudo nano /etc/fail2ban/jail.local
Configure SSH protection in jail.local:
[sshd]
enabled = true
port = 22 # Or your custom SSH port
logpath = /var/log/auth.log
maxretry = 3
bantime = 3600
findtime = 600
Start and enable Fail2Ban:
sudo systemctl start fail2ban
sudo systemctl enable fail2ban
sudo fail2ban-client status sshd
Step 8: Configure Time Synchronization
Accurate system time is critical for logs, SSL certificates, and distributed systems. Every Ubuntu server setup 2026 should configure NTP:
# Ubuntu uses systemd-timesyncd by default
sudo timedatectl set-timezone America/New_York # Or your timezone
sudo timedatectl set-ntp true
# Verify time synchronization
timedatectl status
Step 9: Harden System Settings
Apply additional kernel and network security settings for production Ubuntu server setup 2026:
sudo nano /etc/sysctl.conf
Add these hardening settings:
# IP Spoofing protection
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.default.rp_filter = 1
# Ignore ICMP redirects
net.ipv4.conf.all.accept_redirects = 0
net.ipv6.conf.all.accept_redirects = 0
# Ignore send redirects
net.ipv4.conf.all.send_redirects = 0
# Disable source packet routing
net.ipv4.conf.all.accept_source_route = 0
net.ipv6.conf.all.accept_source_route = 0
# Log Martians
net.ipv4.conf.all.log_martians = 1
Apply settings:
sudo sysctl -p
Step 10: Install Essential Administration Tools
Complete your Ubuntu server setup 2026 with essential utilities:
sudo apt install -y \
htop \
ncdu \
net-tools \
curl \
wget \
git \
vim \
tree \
tmux \
build-essential
Production-Ready Disk Partitioning
For advanced Ubuntu server setup 2026 scenarios, use separate partitions for better security and reliability:
- / (root) – 20-50GB
- /boot – 1GB
- /home – Variable (user data)
- /var – 20GB+ (logs, databases)
- /tmp – 5-10GB (temporary files)
- swap – 2x RAM or 4GB minimum
This partitioning scheme prevents log files from filling the root partition and causing system failures.
External Resources for Ubuntu Server Setup 2026
Expand your Ubuntu server setup 2026 knowledge with these authoritative resources:
- DigitalOcean Ubuntu Initial Server Setup – Comprehensive setup guide
- Ubuntu Official Server Documentation – Canonical’s official tutorials
- Sunlight Media Ubuntu Server First-Time Setup – Beginner-friendly walkthrough
Related Server Administration Guides
Continue building your Linux server skills with these related tutorials:
- Ubuntu Server Security Hardening 2026: Complete Step-by-Step Guide
- How to Set Up SSH Key Authentication on Ubuntu Server 2026
- OpenClaw AI Automation Setup Guide (2026): Install Your Personal AI Assistant
Verification Checklist
Use this checklist to verify your Ubuntu server setup 2026 is complete:
- ✅ System fully updated (
sudo apt update && sudo apt upgrade) - ✅ Non-root sudo user created and tested
- ✅ SSH key authentication working
- ✅ SSH password authentication disabled
- ✅ SSH root login disabled
- ✅ UFW firewall enabled with necessary ports
- ✅ Unattended upgrades configured
- ✅ Fail2Ban active and monitoring SSH
- ✅ System time synchronized with NTP
- ✅ Kernel security parameters applied
- ✅ Essential admin tools installed
Common Ubuntu Server Setup 2026 Troubleshooting
SSH Connection Refused
If you can’t connect via SSH after Ubuntu server setup 2026 configuration:
# Check SSH service status
sudo systemctl status ssh
# Restart SSH
sudo systemctl restart ssh
# Check firewall rules
sudo ufw status
Locked Out After Disabling Password Authentication
If you disabled password auth but SSH keys aren’t working:
- Access server via console (physical or cloud provider’s web console)
- Re-enable password authentication temporarily in
/etc/ssh/sshd_config - Restart SSH:
sudo systemctl restart ssh - Fix your SSH key configuration
- Test key authentication thoroughly
- Disable password authentication again
UFW Blocking Legitimate Traffic
Check UFW logs and rules:
sudo ufw status numbered
sudo tail -f /var/log/ufw.log
# Delete rule by number if needed
sudo ufw delete 3
# Add missing rule
sudo ufw allow 3306/tcp # Example: MySQL
Next Steps After Ubuntu Server Setup 2026
After completing this Ubuntu server setup 2026 guide, your server is production-ready. Consider these next steps:
- Install your application stack – LAMP, LEMP, Node.js, Python, etc.
- Configure backup automation – Use rsync, Duplicity, or cloud backup solutions
- Set up monitoring – Install Prometheus, Grafana, or Netdata
- Implement log aggregation – Configure rsyslog or journald forwarding
- Enable SELinux or AppArmor – Additional mandatory access control
- Configure reverse proxy – Nginx or Apache for web applications
- Set up SSL certificates – Use Let’s Encrypt for HTTPS
Conclusion
Completing a thorough Ubuntu server setup 2026 is the foundation of secure, reliable Linux infrastructure. By following this guide, you’ve configured SSH key authentication, enabled firewall protection, set up automatic security updates, implemented intrusion prevention with Fail2Ban, and hardened system settings—all critical components of production-ready server deployment.
The time invested in proper Ubuntu server setup 2026 pays dividends in security, stability, and ease of management. Your server is now protected against common attack vectors like brute-force SSH attempts, has a solid foundation for deploying applications, and will automatically receive security updates to stay protected against emerging threats.
Remember that server security is an ongoing process, not a one-time configuration. Regularly review your Ubuntu server setup 2026 configuration, monitor security advisories for Ubuntu 24.04 LTS, and keep your system updated. With this solid foundation, you’re ready to build and deploy production applications on Ubuntu Server with confidence.
For additional server hardening, explore our related guides on SSH key authentication, security hardening, and automated deployment workflows. Happy Ubuntu server administration in 2026!
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.