Setting up an ubuntu server initial setup correctly is crucial for security, performance, and long-term maintainability. In 2026, with enhanced security features like Rust-based sudo and post-quantum SSH, Ubuntu Server offers a robust foundation for modern infrastructure. This comprehensive guide walks you through every step of configuring your first Ubuntu Server system from scratch.
Why Initial Server Configuration Matters
A fresh Ubuntu Server installation is functional but not production-ready. Critical security hardening, user account setup, and basic networking configuration are essential to prevent unauthorized access and ensure system reliability. Proper initial setup includes:
- Creating non-root user accounts with sudo privileges
- Configuring SSH key authentication to eliminate password attacks
- Setting up firewall rules to restrict network access
- Updating system packages to patch known vulnerabilities
Prerequisites for Ubuntu Server Setup
Before beginning the ubuntu server initial setup, ensure you have:
- Ubuntu Server 25.10 or later ISO downloaded
- Physical server or virtual machine with minimum 2GB RAM, 25GB storage
- Network connectivity (Ethernet or WiFi)
- Root or administrative access to the server
Step 1: Install Ubuntu Server with Subiquity Installer
Ubuntu Server 2026 uses the Subiquity text-based installer, which provides an intuitive guided setup:
- Boot from installation media: Select “Install Ubuntu Server” from the boot menu
- Choose language and keyboard layout: Select your preferred options
- Configure network: The installer auto-detects network interfaces and configures DHCP by default
- Set up storage: Choose between automatic partitioning (recommended for beginners) or manual setup with LVM/ZFS encryption
- Create initial user account: Provide username, hostname, and password (this will be your primary admin account)
- Enable OpenSSH Server: Check this option to enable remote SSH access immediately
- Select featured snaps (optional): Pre-install tools like Docker, MicroK8s, Nextcloud, or PowerShell
The installer handles partitioning, package installation, and bootloader configuration automatically.
Step 2: First Login and System Updates
After installation completes and the system reboots, log in with the account you created:
ssh username@server-ip-address
Immediately update all packages to patch security vulnerabilities:
sudo apt update
sudo apt upgrade -y
sudo apt dist-upgrade -y
sudo apt autoremove -y
Enable automatic security updates for critical patches:
sudo apt install unattended-upgrades -y
sudo dpkg-reconfigure -plow unattended-upgrades
Step 3: Create a Dedicated Administrative User
If you installed with the root account enabled, create a non-root administrative user immediately:
# Create new user
sudo adduser adminuser
# Add user to sudo group for administrative privileges
sudo usermod -aG sudo adminuser
# Verify sudo access
su - adminuser
sudo whoami
# Should output: root
Step 4: Configure SSH Key-Based Authentication
Password authentication is vulnerable to brute-force attacks. SSH keys provide cryptographically secure authentication:
On your local machine (not the server):
# Generate ED25519 key pair (recommended in 2026)
ssh-keygen -t ed25519 -C "your_email@example.com"
# Copy public key to server
ssh-copy-id adminuser@server-ip-address
On the server, disable password authentication:
sudo nano /etc/ssh/sshd_config
Modify these lines:
PermitRootLogin no
PasswordAuthentication no
PubkeyAuthentication yes
ChallengeResponseAuthentication no
Restart SSH service to apply changes:
sudo systemctl restart sshd
Test SSH key login from a new terminal before closing your current session!
Step 5: Set Up UFW Firewall
Ubuntu’s Uncomplicated Firewall (UFW) provides simple firewall management:
# Allow SSH before enabling firewall (CRITICAL!)
sudo ufw allow OpenSSH
# Enable firewall
sudo ufw enable
# Check status
sudo ufw status verbose
Add rules for services you’ll run:
# Web server
sudo ufw allow 80/tcp
sudo ufw allow 443/tcp
# Custom application port
sudo ufw allow 8080/tcp
Step 6: Configure System Timezone and Hostname
Set the correct timezone for accurate logs and scheduled tasks:
# List available timezones
timedatectl list-timezones
# Set timezone
sudo timedatectl set-timezone Europe/Berlin
# Verify
timedatectl
Update hostname if needed:
sudo hostnamectl set-hostname new-hostname
Step 7: Harden Security with Fail2Ban
Fail2Ban monitors logs and bans IPs with suspicious activity (brute-force attempts):
sudo apt install fail2ban -y
# Create local configuration
sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
sudo nano /etc/fail2ban/jail.local
Configure SSH jail:
[sshd]
enabled = true
port = ssh
logpath = /var/log/auth.log
maxretry = 3
bantime = 3600
Restart Fail2Ban:
sudo systemctl restart fail2ban
sudo systemctl enable fail2ban
Step 8: Enable and Configure TPM-Backed Full Disk Encryption (New in 2026)
Ubuntu Server 2026 introduces experimental TPM-backed Full Disk Encryption for password-less secure booting on supported hardware:
# Check if TPM is available
sudo dmesg | grep -i tpm
# Enable during installation or post-install with:
sudo apt install cryptsetup tpm2-tools
sudo systemctl enable tpm2-abrmd
Note: This feature requires compatible TPM 2.0 hardware and is experimental as of 2026.
Step 9: Set Up Monitoring and Logging
Install basic monitoring tools to track system health:
# Install monitoring utilities
sudo apt install htop iotop nethogs -y
# Check system logs
sudo journalctl -xe
sudo journalctl -u sshd
Consider installing more advanced monitoring:
# Install Netdata for real-time monitoring
bash <(curl -Ss https://my-netdata.io/kickstart.sh)
Step 10: Configure Automatic Backups
Set up automated backups for critical data:
# Install backup tools
sudo apt install rsync borgbackup -y
# Example daily backup script
sudo nano /usr/local/bin/daily-backup.sh
#!/bin/bash
BACKUP_DIR="/var/backups/daily"
DATE=$(date +%Y-%m-%d)
rsync -av /etc/ "$BACKUP_DIR/etc-$DATE/"
rsync -av /home/ "$BACKUP_DIR/home-$DATE/"
sudo chmod +x /usr/local/bin/daily-backup.sh
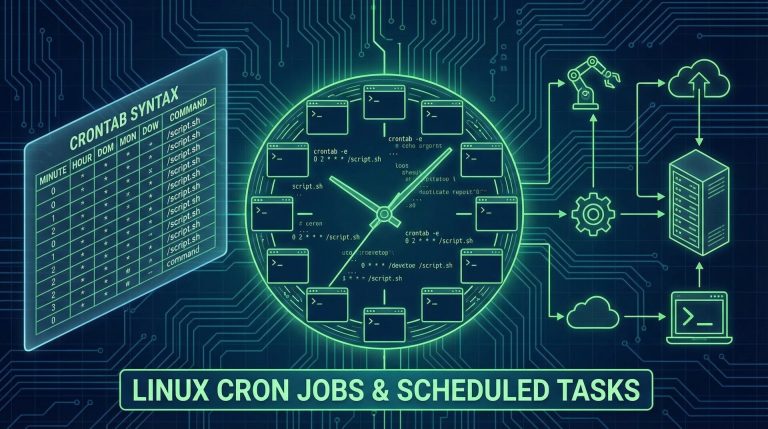
# Add to crontab
sudo crontab -e
# Add line: 0 2 * * * /usr/local/bin/daily-backup.sh
Step 11: Install Essential Software Packages
Install commonly needed utilities:
sudo apt install -y \
curl wget git vim nano \
build-essential software-properties-common \
ca-certificates gnupg lsb-release \
net-tools dnsutils iputils-ping
Step 12: Verify and Test Your Setup
Run through this checklist to ensure everything is configured correctly:
- ✅ SSH key authentication works (passwords disabled)
- ✅ Firewall is active and SSH port is allowed
- ✅ Non-root user has sudo privileges
- ✅ System is fully updated
- ✅ Automatic security updates are enabled
- ✅ Fail2Ban is active and monitoring SSH
- ✅ Timezone is correctly set
- ✅ Basic monitoring tools are installed
# Quick verification commands
sudo ufw status
systemctl status fail2ban
sudo fail2ban-client status sshd
timedatectl
sudo apt list --upgradable
Common Initial Setup Issues and Solutions
Problem: SSH connection refused after disabling password authentication
Solution: Ensure you copied your SSH public key correctly before disabling passwords. Use a backup console access if locked out.
Problem: Firewall blocks legitimate services
Solution: Always allow SSH (port 22) before enabling UFW. Check rules with sudo ufw status numbered.
Problem: Automatic updates cause unexpected reboots
Solution: Configure unattended-upgrades to only install security patches, not all updates.
Next Steps After Initial Setup
With your ubuntu server initial setup complete, you can proceed to:
- Install web servers (Apache, Nginx)
- Set up databases (PostgreSQL, MySQL, MariaDB)
- Configure containerization (Docker, LXD, Kubernetes)
- Deploy applications and services
- Implement advanced security hardening (AppArmor, SELinux)
Conclusion
A proper ubuntu server initial setup is the foundation of a secure, reliable infrastructure. By following these 2026 best practices—creating non-root users, enabling SSH keys, configuring firewalls, and implementing monitoring—you've built a hardened server ready for production workloads. Remember to regularly review security logs, apply updates promptly, and backup your configuration files.
Your Ubuntu Server is now ready to serve whatever mission you have in mind!
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.