Linux server security hardening is essential for protecting your Ubuntu or Debian systems from modern cyber threats. In 2026, with increasing sophisticated attacks targeting Linux infrastructure, implementing comprehensive security measures has never been more critical. This guide covers proven Linux server security hardening techniques specifically for Ubuntu and Debian systems, helping you secure your servers against unauthorized access, malware, and data breaches.
Why Linux Server Security Hardening Matters in 2026
Linux servers power a significant portion of the internet’s infrastructure, making them prime targets for attackers. Linux server security hardening is not just about installing a firewall; it is a comprehensive approach to reducing your attack surface and implementing defense-in-depth strategies.
Recent security reports show that unhardened Linux servers face attacks within hours of being connected to the internet. Implementing proper Linux server security hardening measures can reduce your risk by over 90 percent according to cybersecurity researchers.
Initial Linux Server Security Hardening Steps
Update Your System
The foundation of Linux server security hardening begins with keeping your system updated. Before implementing any other security measures, ensure all packages are current:
sudo apt update sudo apt upgrade -y
For Ubuntu 26.04 and Debian 12, security patches are released regularly. Configure automatic security updates as part of your Linux server security hardening strategy:
sudo apt install unattended-upgrades sudo dpkg-reconfigure unattended-upgrades
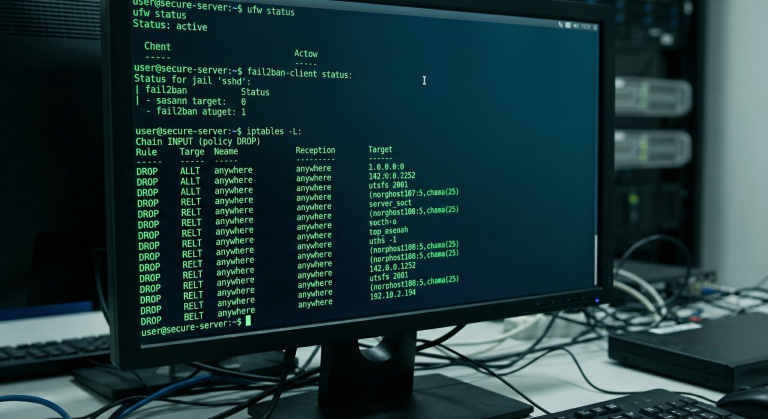
Configure the Firewall
UFW (Uncomplicated Firewall) is the standard firewall tool for Ubuntu and Debian. Effective Linux server security hardening requires a default-deny policy:
sudo ufw default deny incoming sudo ufw default allow outgoing sudo ufw allow ssh sudo ufw enable
Only open ports that are absolutely necessary for your services. Each open port increases your attack surface and requires additional Linux server security hardening considerations.
Secure SSH Access
SSH is the most common attack vector for Linux servers. Linux server security hardening for SSH includes several critical steps:
First, disable root login via SSH. Edit /etc/ssh/sshd_config:
PermitRootLogin no PasswordAuthentication no PubkeyAuthentication yes
Use SSH keys instead of passwords. Generate a key pair on your local machine:
ssh-keygen -t ed25519 -C "your-email@example.com" ssh-copy-id user@server-ip
Change the default SSH port to reduce automated attacks:
Port 2222
Remember to update your firewall rules when changing the SSH port as part of your Linux server security hardening.
Advanced Linux Server Security Hardening Techniques
Install and Configure Fail2Ban
Fail2Ban is essential for Linux server security hardening. It monitors log files and bans IP addresses that show malicious behavior:
sudo apt install fail2ban sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
Edit /etc/fail2ban/jail.local for your Linux server security hardening needs:
[sshd] enabled = true port = ssh filter = sshd logpath = /var/log/auth.log maxretry = 3 bantime = 3600
Restart Fail2Ban to apply your Linux server security hardening changes:
sudo systemctl restart fail2ban
Implement Mandatory Access Control
AppArmor is the default MAC (Mandatory Access Control) system for Ubuntu and an important part of Linux server security hardening. It confines programs to a limited set of resources:
sudo aa-status
For Debian, you may need to install AppArmor:
sudo apt install apparmor apparmor-profiles sudo systemctl enable apparmor
SELinux is another option for Linux server security hardening, though it requires more configuration expertise. AppArmor is generally preferred for Ubuntu and Debian due to its easier learning curve.
Disable Unnecessary Services
Every running service is a potential attack vector. Effective Linux server security hardening involves auditing and disabling unused services:
sudo systemctl list-unit-files --type=service --state=enabled
Disable services you do not need:
sudo systemctl disable service-name sudo systemctl stop service-name
Common candidates for removal in Linux server security hardening include:
- CUPS (printing services)
- Avahi (mDNS/DNS-SD)
- Bluetooth services
- ModemManager
User and Permission Management for Linux Server Security Hardening
Create Limited User Accounts
Linux server security hardening requires proper user management. Create individual user accounts instead of sharing root or a single administrative account:
sudo adduser newusername sudo usermod -aG sudo newusername
Use sudo for administrative tasks rather than logging in as root. This is a fundamental principle of Linux server security hardening.
Implement Strong Password Policies
Configure password policies as part of your Linux server security hardening:
sudo apt install libpam-pwquality
Edit /etc/security/pwquality.conf:
minlen = 14 minclass = 3 maxrepeat = 2
Set Up Two-Factor Authentication
For enhanced Linux server security hardening, implement two-factor authentication for SSH:
sudo apt install libpam-google-authenticator
Have each user run google-authenticator and follow the setup process. Then configure PAM and SSH to require the second factor.
Network Security in Linux Server Security Hardening
Configure TCP Wrappers
TCP wrappers add another layer to your Linux server security hardening by controlling access to network services:
Edit /etc/hosts.allow:
sshd: 192.168.1.0/24
Edit /etc/hosts.deny:
ALL: ALL
Implement Network Segmentation
For multi-server environments, Linux server security hardening should include network segmentation. Use VLANs or separate subnets to isolate different services:
- Web servers in one segment
- Database servers in another
- Management interfaces on a separate network
Configure Intrusion Detection
AIDE (Advanced Intrusion Detection Environment) monitors file integrity as part of Linux server security hardening:
sudo apt install aide sudo aideinit
Schedule regular integrity checks:
0 3 * * * /usr/bin/aide.wrapper --check
Logging and Monitoring for Linux Server Security Hardening
Centralize Log Management
Effective Linux server security hardening requires comprehensive logging. Configure rsyslog or use modern alternatives like journald:
sudo systemctl status systemd-journald
For multiple servers, consider a centralized logging solution like ELK stack or Graylog as part of your Linux server security hardening strategy.
Set Up Log Rotation
Prevent log files from consuming disk space:
sudo logrotate -d /etc/logrotate.conf
Custom log rotation rules can be added to /etc/logrotate.d/.
Monitor for Security Events
Install and configure auditd for detailed system call monitoring:
sudo apt install auditd sudo auditctl -e 1
Add audit rules for critical files as part of your Linux server security hardening:
-w /etc/passwd -p wa -k identity -w /etc/group -p wa -k identity
Application-Level Linux Server Security Hardening
Secure Web Servers
If running Apache or Nginx, application-specific Linux server security hardening is essential:
For Nginx:
server_tokens off; add_header X-Frame-Options "SAMEORIGIN"; add_header X-Content-Type-Options "nosniff";
Hide version information and implement security headers as part of comprehensive Linux server security hardening.
Database Security
For MySQL/MariaDB or PostgreSQL:
sudo mysql_secure_installation
Key Linux server security hardening steps for databases include:
- Removing anonymous users
- Disabling remote root access
- Removing test databases
- Using strong authentication
Container Security
If using Docker or Podman, Linux server security hardening extends to container configurations:
docker run --read-only --security-opt=no-new-privileges image
Run containers with minimal privileges and read-only filesystems where possible.
Automated Linux Server Security Hardening Tools
OpenSCAP and CIS Benchmarks
Automate Linux server security hardening with OpenSCAP:
sudo apt install libopenscap8 scap-workbench
Download and apply CIS benchmarks for Ubuntu or Debian:
oscap xccdf eval --profile xccdf_org.ssgproject.content_profile_cis_level1_server \ --results scan-results.xml \ /usr/share/xml/scap/ssg/content/ssg-ubuntu2204-ds.xml
Lynis Security Auditing
Lynis provides comprehensive Linux server security hardening assessments:
sudo apt install lynis sudo lynis audit system
Review the report and implement recommended Linux server security hardening measures.
Regular Maintenance for Ongoing Linux Server Security Hardening
Security Patch Management
Linux server security hardening is an ongoing process. Subscribe to security mailing lists:
- Ubuntu Security Notices
- Debian Security Advisory
- US-CERT alerts
Test patches in a staging environment before production deployment.
Periodic Security Audits
Schedule regular security assessments:
sudo lynis audit system --quick
Review and update your Linux server security hardening configurations quarterly.
Backup and Recovery
No Linux server security hardening strategy is complete without backups:
rsync -avz --delete /critical/data backup-server:/backups/
Test restoration procedures regularly. A backup you cannot restore is useless.
Compliance and Linux Server Security Hardening
Depending on your industry, Linux server security hardening may need to meet specific standards:
- GDPR for EU data protection
- HIPAA for healthcare
- PCI-DSS for payment processing
- SOC 2 for service organizations
Document your Linux server security hardening procedures for compliance audits.
Conclusion
Linux server security hardening for Ubuntu and Debian requires a multi-layered approach. From basic system updates to advanced intrusion detection, each layer adds protection against potential threats.
Start with the fundamentals: updates, firewall configuration, and SSH hardening. Gradually implement advanced Linux server security hardening measures like Fail2Ban, AppArmor, and centralized logging.
Remember that Linux server security hardening is not a one-time task but an ongoing process. Regular audits, patch management, and monitoring are essential for maintaining a secure server environment in 2026 and beyond.
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.