This comprehensive ubuntu 26.04 lts server setup guide walks you through every step of deploying a secure, production-ready server in 2026. Whether you’re managing a small business infrastructure, hosting web applications, or building a development environment, Ubuntu 26.04 LTS (codenamed “Resolute Raccoon”) offers the stability and long-term support that mission-critical systems demand. By following this tutorial, you’ll have a hardened server that follows industry best practices for security and performance.
Why Choose Ubuntu 26.04 LTS for Your Server?
Ubuntu’s Long Term Support (LTS) releases provide five years of security updates and maintenance, making them the preferred choice for production environments. The ubuntu 26.04 lts server setup process builds upon the solid foundation of previous releases while introducing several improvements for modern workloads.
Key advantages of Ubuntu 26.04 LTS include enhanced kernel security features, improved container support, updated software repositories, and better hardware compatibility with the latest server platforms. The LTS designation means you can deploy with confidence, knowing your infrastructure will receive critical security patches until 2031.
Pre-Installation Checklist
Before beginning your ubuntu 26.04 lts server setup, ensure you have:
- A server or virtual machine with at least 2 CPU cores and 4GB RAM (8GB+ recommended for production)
- 20GB of available disk space minimum (100GB+ recommended)
- Ubuntu 26.04 LTS ISO image downloaded from the official Ubuntu website
- Network access with a static IP configuration planned
- SSH client for remote access after installation
- Backup of any existing data if upgrading from a previous version
Step 1: Installing Ubuntu 26.04 LTS Server
Boot from Installation Media
Start your server with the Ubuntu 26.04 LTS installation media. The boot menu offers several options; select “Try or Install Ubuntu Server” to begin the ubuntu 26.04 lts server setup process. For automated deployments across multiple machines, consider using the autoinstall feature with a cloud-init configuration.
Language and Keyboard Configuration
Select your preferred language for the installation process. For server deployments, English is commonly chosen for consistency across team members. Configure your keyboard layout carefully, as this affects command-line interactions after installation.
Network Configuration
During the ubuntu 26.04 lts server setup, configure your network interface with a static IP address for production servers. While DHCP works for testing, static addressing ensures consistent connectivity and simplifies firewall rules:
Subnet: 192.168.1.0/24
Address: 192.168.1.100
Gateway: 192.168.1.1
Name servers: 1.1.1.1, 8.8.8.8Storage Configuration
For most ubuntu 26.04 lts server setup scenarios, use the entire disk with LVM (Logical Volume Management) enabled. LVM provides flexibility for future storage expansion and snapshot capabilities. If you have specific partitioning requirements, manual configuration allows separate partitions for /boot, /, /var, and /home.
User Account Setup
Create a non-root user with sudo privileges. Never use the root account for daily operations. Choose a strong, unique password and consider setting up SSH key authentication immediately after installation for enhanced security.
SSH Server and Featured Server Snaps
During installation, ensure OpenSSH server is selected to enable remote management. For a minimal ubuntu 26.04 lts server setup, avoid installing additional snaps unless specifically needed. You can always add software later using apt or snap commands.
Step 2: Post-Installation Configuration
Once the installation completes and your server reboots, log in and perform these essential configuration steps:
Update System Packages
sudo apt update
sudo apt upgrade -y
sudo apt autoremove -yKeeping your system updated is the foundation of server security. These commands ensure you have the latest security patches and bug fixes immediately after your ubuntu 26.04 lts server setup.
Configure Hostname and Timezone
sudo hostnamectl set-hostname your-server-name
sudo timedatectl set-timezone Europe/Berlin
sudo apt install chrony -yAccurate timekeeping is essential for log correlation, SSL certificate validation, and distributed systems. Chrony provides better time synchronization than the traditional ntpd service.
Set Up SSH Key Authentication
Disable password-based SSH authentication and use keys instead. This dramatically improves security:
# On your local machine, generate a key pair
ssh-keygen -t ed25519 -C "your-email@example.com"
# Copy the public key to your server
ssh-copy-id user@server-ip
# Edit SSH configuration
sudo nano /etc/ssh/sshd_configModify these settings in sshd_config for a secure ubuntu 26.04 lts server setup:
PermitRootLogin no
PasswordAuthentication no
PubkeyAuthentication yes
MaxAuthTries 3
ClientAliveInterval 300
ClientAliveCountMax 2sudo systemctl restart sshdFor more details on SSH hardening, refer to our SSH Security Hardening Guide.
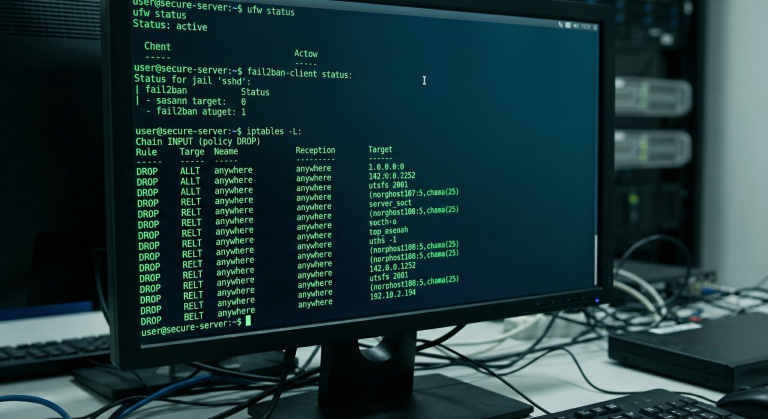
Step 3: Firewall Configuration with UFW
Ubuntu’s Uncomplicated Firewall (UFW) provides an easy-to-use interface for iptables. A properly configured firewall is essential for any production ubuntu 26.04 lts server setup:
# Install UFW if not present
sudo apt install ufw -y
# Set default policies
sudo ufw default deny incoming
sudo ufw default allow outgoing
# Allow SSH (adjust port if you've changed it)
sudo ufw allow 22/tcp
# Allow common services if needed
sudo ufw allow 80/tcp # HTTP
sudo ufw allow 443/tcp # HTTPS
# Enable the firewall
sudo ufw enableVerify your rules with sudo ufw status verbose before enabling. Always ensure you have an active SSH session before enabling UFW to prevent lockouts. Learn more in our UFW Firewall Configuration Tutorial.
Step 4: Automatic Security Updates
Enable unattended-upgrades to automatically install security patches. This is critical for maintaining a secure ubuntu 26.04 lts server setup without manual intervention:
sudo apt install unattended-upgrades -y
sudo dpkg-reconfigure -plow unattended-upgradesConfigure the upgrade behavior:
sudo nano /etc/apt/apt.conf.d/50unattended-upgradesEnsure these lines are uncommented for automatic security updates:
Unattended-Upgrade::Allowed-Origins {
"${distro_id}:${distro_codename}-security";
"${distro_id}ESMApps:${distro_codename}-apps-security";
"${distro_id}ESM:${distro_codename}-infra-security";
};Step 5: Install and Configure Fail2ban
Fail2ban protects your server from brute-force attacks by monitoring logs and banning suspicious IP addresses. It’s an essential component of any ubuntu 26.04 lts server setup:
sudo apt install fail2ban -y
sudo systemctl enable fail2ban
sudo systemctl start fail2banCreate a custom configuration:
sudo nano /etc/fail2ban/jail.local[DEFAULT]
bantime = 1h
findtime = 10m
maxretry = 3
[sshd]
enabled = true
port = 22
filter = sshd
logpath = /var/log/auth.log
maxretry = 3sudo systemctl restart fail2ban
sudo fail2ban-client statusStep 6: Additional Security Hardening
Disable IPv6 (if not needed)
sudo nano /etc/sysctl.confnet.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.disable_ipv6 = 1sudo sysctl -pKernel Hardening with Sysctl
Create a security-focused sysctl configuration:
sudo nano /etc/sysctl.d/99-security.conf# Disable IP source routing
net.ipv4.conf.all.accept_source_route = 0
net.ipv6.conf.all.accept_source_route = 0
# Disable ICMP redirects
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.all.secure_redirects = 0
# Enable SYN flood protection
net.ipv4.tcp_syncookies = 1
# Disable IPv4 forwarding (unless using as router)
net.ipv4.ip_forward = 0sudo sysctl -p /etc/sysctl.d/99-security.confInstall and Configure AIDE
AIDE (Advanced Intrusion Detection Environment) monitors file integrity:
sudo apt install aide -y
sudo aideinit
sudo mv /var/lib/aide/aide.db.new /var/lib/aide/aide.dbStep 7: Monitoring and Logging
Install Logwatch
sudo apt install logwatch -yConfigure Log Rotation
sudo nano /etc/logrotate.confEnsure log rotation is enabled to prevent disk space issues. Ubuntu 26.04 LTS comes with sensible defaults, but review them for your specific retention requirements.
Set Up Audit Logging
sudo apt install auditd -y
sudo systemctl enable auditd
sudo auditctl -e 1For more monitoring solutions, check our guide on Linux Server Monitoring Tools.
Step 8: Backup Strategy
No ubuntu 26.04 lts server setup is complete without a backup strategy. Install and configure Restic for encrypted backups:
sudo apt install restic -y
# Initialize backup repository
restic init --repo /backup/repoCreate a backup script:
#!/bin/bash
# /usr/local/bin/backup.sh
export RESTIC_REPOSITORY="/backup/repo"
export RESTIC_PASSWORD="your-secure-password"
restic backup /etc /home /var/www
restic forget --keep-daily 7 --keep-weekly 4 --keep-monthly 12
restic prunechmod +x /usr/local/bin/backup.shAdd to crontab for automated daily backups:
0 2 * * * /usr/local/bin/backup.shUbuntu 26.04 LTS Server Setup Checklist
Use this checklist to verify your ubuntu 26.04 lts server setup is complete:
- ☐ Operating system installed with latest updates
- ☐ Static IP configuration active
- ☐ Hostname and timezone configured
- ☐ Non-root user with sudo privileges created
- ☐ SSH key authentication enabled, password auth disabled
- ☐ Firewall (UFW) enabled with appropriate rules
- ☐ Automatic security updates configured
- ☐ Fail2ban installed and configured
- ☐ Kernel security parameters applied via sysctl
- ☐ File integrity monitoring (AIDE) installed
- ☐ Audit logging enabled
- ☐ Backup solution configured and tested
Troubleshooting Common Issues
SSH Connection Refused
If you cannot connect via SSH after your ubuntu 26.04 lts server setup, verify:
- OpenSSH server is installed:
sudo systemctl status ssh - Firewall allows SSH port:
sudo ufw status - Correct IP address and port
- Network connectivity from client
Package Installation Failures
sudo apt update --fix-missing
sudo apt install -fFirewall Lockout
If UFW blocks your SSH access, use your hosting provider’s console access to disable it:
sudo ufw disableConclusion
This ubuntu 26.04 lts server setup guide has covered the essential steps for deploying a secure, production-ready Ubuntu server. From initial installation through comprehensive security hardening, you now have a server configured following industry best practices.
Remember that security is an ongoing process, not a one-time configuration. Regularly review logs, keep your system updated, and periodically audit your security posture. Ubuntu 26.04 LTS provides an excellent foundation for reliable server infrastructure with five years of support ahead.
By following this tutorial, your server is now protected against common attack vectors while maintaining the flexibility to host applications, websites, or services. Continue exploring advanced topics like containerization with Docker, orchestration with Kubernetes, or automation with Ansible to further enhance your infrastructure capabilities.
Additional Resources
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.