Docker container security best practices are essential for protecting production workloads from vulnerabilities, privilege escalation attacks, and container escape threats. In 2026, with new CVEs affecting container runtimes and the increasing sophistication of supply chain attacks, implementing comprehensive security measures has never been more critical. This guide covers every aspect of securing Docker containers, from image hardening to runtime protection.
Why Docker Container Security Matters in 2026
Container adoption has accelerated dramatically, but security often lags behind deployment speed. Recent vulnerabilities like CVE-2025-68121 in Docker Engine highlight the ongoing risks facing containerized applications. Docker container security best practices protect against these threats while ensuring compliance with security frameworks and regulatory requirements.
Containers share the host kernel, making kernel-level vulnerabilities potentially catastrophic. A compromised container can lead to full host access if proper isolation mechanisms are not in place. Understanding and implementing security layers—from image creation to runtime enforcement—is essential for production deployments.
Step 1: Harden Your Container Images
Security starts with the images you build and deploy. Docker container security best practices demand minimal, frequently updated base images with no unnecessary components. Start with official, trusted images and remove everything not required for your application.
Use minimal base images to reduce attack surface. Alpine Linux provides a lightweight foundation at approximately 5MB, while distroless images from Google eliminate package managers and shells entirely:
# Good: Minimal Alpine base
FROM alpine:3.19
# Better: Distroless for production
FROM gcr.io/distroless/nodejs20-debian12Avoid using :latest tags in production. Pin specific image versions and update deliberately after testing:
# Bad
FROM node:latest
# Good
FROM node:20.11.0-alpine3.19Scan images for vulnerabilities before deployment. Tools like Trivy, Clair, and Anchore identify known CVEs in your container layers:
# Install Trivy
sudo apt install trivy
# Scan an image
trivy image myapp:1.0.0Multi-stage builds reduce final image size by separating build dependencies from runtime requirements:
# Build stage
FROM node:20-alpine AS builder
WORKDIR /app
COPY package*.json ./
RUN npm ci
COPY . .
RUN npm run build
# Production stage
FROM node:20-alpine
WORKDIR /app
COPY --from=builder /app/dist ./dist
COPY --from=builder /app/node_modules ./node_modules
EXPOSE 3000
CMD ["node", "dist/main.js"]Step 2: Run Containers as Non-Root Users
Running containers as root provides attackers with immediate privileged access if they escape the container. Docker container security best practices require creating dedicated users with minimal permissions:
FROM alpine:3.19
# Create non-root user
RUN addgroup -g 1001 appgroup && \
adduser -u 1001 -G appgroup -s /bin/sh -D appuser
# Switch to non-root user
USER appuser
WORKDIR /home/appuser
COPY --chown=appuser:appgroup . .
CMD ["./myapp"]Verify your container runs without root privileges:
docker run --rm myapp id
# Should show: uid=1001(appuser) gid=1001(appgroup)Enforce this at runtime with the –user flag:
docker run --user 1001:1001 myappStep 3: Implement Linux Security Features
Docker leverages Linux kernel security features to isolate containers. Properly configuring these mechanisms is fundamental to Docker container security best practices. Enable and customize Seccomp, AppArmor, and capabilities for defense in depth.
Drop all capabilities and add only those explicitly required:
docker run --cap-drop=ALL --cap-add=NET_BIND_SERVICE nginxCommon capabilities to consider:
- NET_BIND_SERVICE: Bind to privileged ports (less than 1024)
- CHOWN: Change file ownership
- SETGID/SETUID: Change process group/user ID
Disable privilege escalation within containers:
docker run --security-opt no-new-privileges:true myappApply custom Seccomp profiles to restrict available system calls:
docker run --security-opt seccomp=/path/to/custom-seccomp.json myappUse read-only root filesystems to prevent runtime modifications:
docker run --read-only --tmpfs /tmp --tmpfs /var/run myappStep 4: Configure Docker Daemon Security
Global security settings in the Docker daemon configuration apply to all containers. Edit /etc/docker/daemon.json to implement Docker container security best practices at the system level:
sudo nano /etc/docker/daemon.jsonAdd these security-focused configurations:
{
"userns-remap": "default",
"no-new-privileges": true,
"seccomp-profile": "/etc/docker/seccomp-profile.json",
"log-driver": "json-file",
"log-opts": {
"max-size": "10m",
"max-file": "3"
},
"live-restore": true,
"userland-proxy": false,
"icc": false
}Configuration explanations:
- userns-remap: Enable user namespace remapping to isolate container users from host
- no-new-privileges: Prevent processes from gaining additional privileges
- seccomp-profile: Apply custom system call filtering
- log-opts: Limit log file size and rotation
- live-restore: Keep containers running when daemon restarts
- icc: Disable inter-container communication by default
Restart Docker to apply changes:
sudo systemctl restart dockerStep 5: Secure Container Networking
Network segmentation limits the blast radius of compromised containers. Docker container security best practices require custom bridge networks and explicit connection policies rather than the default bridge.
Create isolated networks for different application tiers:
docker network create --driver bridge frontend-net
docker network create --driver bridge backend-netConnect containers only to networks they require:
docker run --network frontend-net nginx
docker run --network backend-net databaseAvoid using –network host which removes network isolation:
# Bad - removes network isolation
docker run --network host myapp
# Good - maintains container network isolation
docker run --publish 8080:80 myappUse iptables or Docker network policies to restrict container-to-container traffic:
# Block outbound traffic except to specific destinations
docker run --iptables=false myappStep 6: Protect Sensitive Data
Never hardcode secrets in Docker images. Docker container security best practices require proper secret management using Docker secrets or external vault solutions:
Use Docker secrets in Swarm mode:
echo "my_secret_password" | docker secret create db_password -
docker service create --secret db_password myappFor Compose deployments:
version: "3.8"
services:
app:
image: myapp
secrets:
- db_password
secrets:
db_password:
file: ./secrets/db_password.txtEnvironment variables appear in process listings and logs. Use secrets mounted as files instead:
# Bad
ENV DB_PASSWORD=secret123
# Good
RUN --mount=type=secret,id=db_password,target=/run/secrets/db_password \
DB_PASSWORD=$(cat /run/secrets/db_password) ./setup.shNever commit .env files or secret mounts to version control. Add them to .gitignore:
.env
secrets/
*.pem
*.keyStep 7: Enable Runtime Monitoring
Continuous monitoring detects anomalies and potential breaches in real-time. Tools like Falco monitor system calls and container behavior, alerting on suspicious activities that violate Docker container security best practices.
Install Falco on your Docker host:
curl -fsSL https://falco.org/repo/falcosecurity-packages.asc | \
sudo gpg --dearmor -o /usr/share/keyrings/falco-archive-keyring.gpg
sudo bash -c 'cat > /etc/apt/sources.list.d/falcosecurity.list <Falco rules detect common attack patterns:
- Unexpected process execution
- Privilege escalation attempts
- File system access outside expected paths
- Sensitive file access (/etc/shadow, etc.)
- Outbound network connections from unexpected processes
Configure Falco to send alerts to your SIEM or notification system for immediate response to potential container compromises.
Step 8: Implement Image Signing and Verification
Supply chain attacks compromise images before they reach your infrastructure. Docker container security best practices include signing images and verifying signatures before deployment:
Enable Docker Content Trust to require signed images:
export DOCKER_CONTENT_TRUST=1Sign your images with Docker Notary before pushing to registries:
docker trust sign myregistry/myapp:1.0.0Inspect image signatures before deployment:
docker trust inspect --pretty myregistry/myapp:1.0.0For comprehensive supply chain security, integrate with Sigstore and Cosign for keyless signing using OIDC identity:
cosign sign --yes myregistry/myapp@sha256:abc123...Step 9: Regular Security Audits
Establish a routine audit process to identify drift from Docker container security best practices. Automated scanning and manual reviews catch configuration errors before they become vulnerabilities.
Create an audit script to check common security misconfigurations:
#!/bin/bash
# Docker Security Audit Script
echo "Checking for privileged containers..."
docker ps --quiet --all | xargs docker inspect --format '{{ .Name }}: Privileged={{ .HostConfig.Privileged }}' | grep "Privileged=true"
echo "Checking for containers running as root..."
docker ps --quiet --all | xargs docker inspect --format '{{ .Name }}: User={{ .Config.User }}' | grep "User=$"
echo "Checking for containers with host networking..."
docker ps --quiet --all | xargs docker inspect --format '{{ .Name }}: NetworkMode={{ .HostConfig.NetworkMode }}' | grep "NetworkMode=host"
echo "Checking for mounted Docker sockets..."
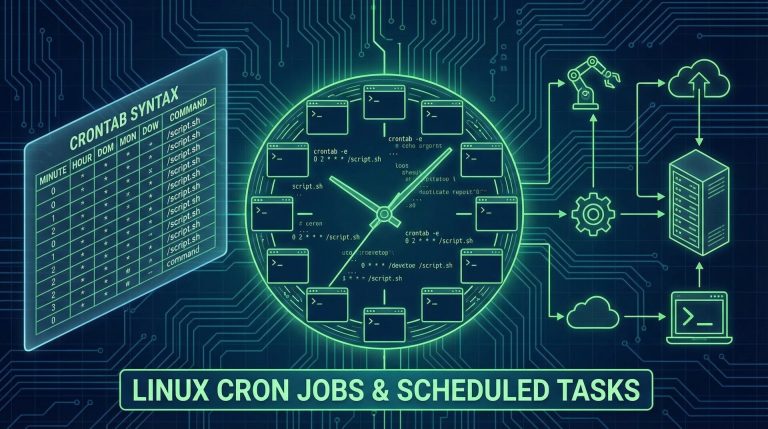
docker ps --quiet --all | xargs docker inspect --format '{{ .Name }}: {{ range .Mounts }}{{ .Source }}:{{ .Destination }} {{ end }}' | grep "/var/run/docker.sock"Schedule regular audits using cron to catch security drift:
0 2 * * * /path/to/docker-security-audit.sh | mail -s "Docker Security Audit" admin@company.comConclusion
Implementing Docker container security best practices requires a defense-in-depth approach spanning the entire container lifecycle. From hardened base images and non-root execution to runtime monitoring and supply chain verification, each layer adds protection against evolving threats.
Security is not a destination but a continuous process. Regularly update your base images, audit configurations, and stay informed about new vulnerabilities affecting container technologies. The practices outlined in this guide provide a solid foundation for securing production Docker deployments in 2026 and beyond.
For additional security resources, explore the Linux Server Hardening Guide and Kubernetes Security Best Practices. The Docker Security Documentation and CIS Docker Benchmark provide authoritative guidance for enterprise deployments.
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.