Ubuntu server security hardening is essential for protecting your infrastructure against modern cyber threats. This comprehensive guide walks you through proven techniques to secure your Ubuntu server, from initial setup to advanced protection measures. Whether you are managing a production web server or a development environment, implementing proper security hardening practices will significantly reduce your attack surface and keep your data safe.
Why Ubuntu Server Security Hardening Matters in 2026
Ubuntu server security hardening has become more critical than ever as cyberattacks continue to evolve in sophistication. According to recent security reports, over 60% of successful breaches exploit misconfigured servers. By following this Ubuntu server security hardening guide, you will implement defense-in-depth strategies that protect against unauthorized access, malware, and data exfiltration. The steps outlined here apply to Ubuntu 22.04 LTS, Ubuntu 24.04 LTS, and newer versions.
Many administrators underestimate the importance of comprehensive Ubuntu server security hardening until they face a security incident. Proactive hardening not only prevents breaches but also ensures compliance with industry standards like PCI DSS, HIPAA, and GDPR. This tutorial covers everything from basic configurations to enterprise-grade security measures.
Initial Server Setup and User Management
Before diving into advanced Ubuntu server security hardening techniques, start with the fundamentals. First, ensure your system is fully updated. Run sudo apt update && sudo apt upgrade -y to install the latest security patches. Keeping your system updated is the foundation of effective Ubuntu server security hardening.
Next, create a dedicated administrative user instead of using root. Add a new user with sudo adduser adminuser and grant sudo privileges with sudo usermod -aG sudo adminuser. This Ubuntu server security hardening practice limits root exposure and provides audit trails for administrative actions. Always disable direct root login via SSH to prevent brute-force attacks targeting the root account.
SSH Hardening for Maximum Security
SSH is the primary attack vector for most Ubuntu servers. Effective Ubuntu server security hardening requires securing SSH access properly. Edit the SSH configuration file at /etc/ssh/sshd_config and implement these changes:
Change the default SSH port from 22 to a non-standard port like 2222 or higher. While this is security through obscurity, it dramatically reduces automated bot attacks. Set PermitRootLogin no to prevent root login attempts. Disable password authentication entirely by setting PasswordAuthentication no and use SSH keys exclusively. This Ubuntu server security hardening step alone blocks 99% of brute-force attempts.
Implement additional SSH hardening by setting MaxAuthTries 3 to limit failed login attempts and ClientAliveInterval 300 to disconnect idle sessions. After making changes, restart SSH with sudo systemctl restart sshd. Always test your SSH configuration in a separate terminal before closing your current session to avoid lockouts.
Configuring UFW Firewall
A properly configured firewall is crucial for Ubuntu server security hardening. Ubuntu includes UFW (Uncomplicated Firewall), which provides an easy-to-use interface for iptables. Start by enabling UFW with sudo ufw enable. Before doing so, configure rules to avoid locking yourself out.
Allow your SSH port first: sudo ufw allow 2222/tcp (or your custom port). Then allow necessary services like HTTP and HTTPS: sudo ufw allow 80/tcp and sudo ufw allow 443/tcp. This Ubuntu server security hardening approach follows the principle of least privilege, only opening ports that are absolutely necessary.
For enhanced protection, configure UFW to limit connection rates: sudo ufw limit 2222/tcp prevents brute-force attacks by blocking IPs that attempt too many connections. Review your firewall status regularly with sudo ufw status verbose and adjust rules as your server requirements evolve.
Installing and Configuring Fail2Ban
Fail2Ban is an essential tool for Ubuntu server security hardening that monitors log files and bans IPs showing malicious patterns. Install it with sudo apt install fail2ban -y. The default configuration provides good protection, but you should customize it for your environment.
Create a local configuration file at /etc/fail2ban/jail.local to override defaults. Configure SSH protection with appropriate ban times and retry limits. For comprehensive Ubuntu server security hardening, enable jails for nginx, Apache, and other services you run. Set bantime = 3600 for one-hour bans and maxretry = 3 to block IPs after three failed attempts.
Monitor Fail2Ban activity with sudo fail2ban-client status and sudo fail2ban-client status sshd to see banned IPs. This Ubuntu server security hardening tool automatically adapts to emerging threats and provides an additional layer of protection beyond your firewall.
Automatic Security Updates
Keeping your server patched is critical for maintaining security. Configure unattended upgrades for automatic security updates as part of your Ubuntu server security hardening strategy. Install the package with sudo apt install unattended-upgrades -y and configure it to automatically install security updates.
Edit /etc/apt/apt.conf.d/50unattended-upgrades to specify which updates to install automatically. Enable automatic reboots if required by kernel updates, scheduling them during maintenance windows. This Ubuntu server security hardening practice ensures critical vulnerabilities are patched promptly without manual intervention.
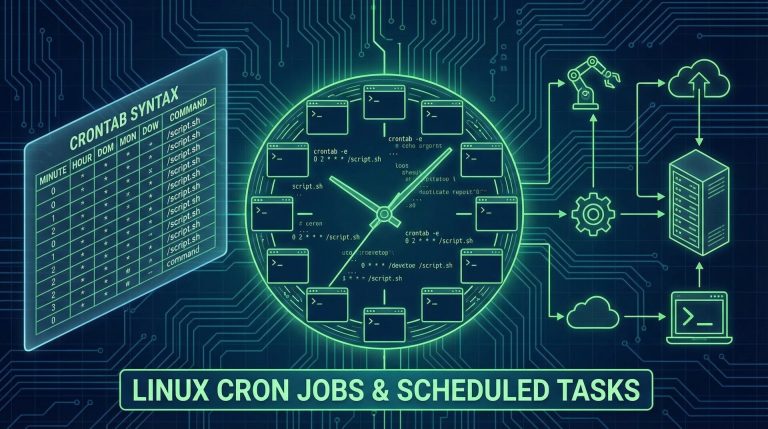
Intrusion Detection with AIDE
AIDE (Advanced Intrusion Detection Environment) monitors your filesystem for unauthorized changes, a crucial component of comprehensive Ubuntu server security hardening. Install it with sudo apt install aide -y and initialize the database with sudo aideinit. This creates a baseline of your system’s normal state.
Schedule regular integrity checks using cron jobs to compare the current system state against the baseline. Any discrepancies indicate potential compromise and should be investigated immediately. This Ubuntu server security hardening technique detects rootkits, backdoors, and unauthorized file modifications that might bypass other security measures.
Kernel Hardening with Sysctl Parameters
Kernel-level Ubuntu server security hardening protects against network-based attacks and information leakage. Configure sysctl parameters in /etc/sysctl.conf or create custom files in /etc/sysctl.d/. Enable SYN cookies to prevent SYN flood attacks: net.ipv4.tcp_syncookies = 1.
Disable IP source routing and ICMP redirects to prevent man-in-the-middle attacks. Enable IP spoofing protection with net.ipv4.conf.all.rp_filter = 1. These Ubuntu server security hardening measures strengthen your network stack against common attack vectors and information disclosure vulnerabilities.
File Permissions and Access Controls
Proper file permissions are fundamental to Ubuntu server security hardening. Apply the principle of least privilege to all files and directories. Sensitive configuration files should be readable only by root: chmod 600 /etc/ssh/sshd_config. Regularly audit permissions with find / -perm -4000 -type f to identify SUID files that might pose security risks.
Consider implementing Access Control Lists (ACLs) for granular permission management. Tools like setfacl and getfacl provide more flexibility than traditional Unix permissions. This Ubuntu server security hardening practice ensures users and processes only have access to resources they genuinely need.
Logging and Monitoring
Comprehensive logging is essential for effective Ubuntu server security hardening and incident response. Centralize logs using rsyslog or specialized tools like ELK stack. Configure log rotation to prevent disk space exhaustion while retaining sufficient history for forensic analysis.
Monitor authentication logs with grep "Failed password" /var/log/auth.log to detect brute-force attempts. Set up real-time alerting for suspicious activities using tools like Logwatch or custom scripts. This Ubuntu server security hardening practice ensures you detect and respond to threats promptly.
Network Security Best Practices
Beyond the firewall, implement network-level Ubuntu server security hardening measures. Disable IPv6 if not needed by adding ipv6.disable=1 to kernel parameters. This reduces your attack surface and simplifies security management. Configure TCP wrappers in /etc/hosts.allow and /etc/hosts.deny for additional access control.
Use network segmentation to isolate critical services. Run databases and sensitive applications on separate network segments with restricted access. This Ubuntu server security hardening strategy limits lateral movement if one server is compromised.
Conclusion: Maintaining Your Security Posture
Ubuntu server security hardening is not a one-time task but an ongoing process. Regularly review and update your security configurations as threats evolve and new vulnerabilities are discovered. Schedule quarterly security audits to verify that your hardening measures remain effective and properly configured.
This comprehensive Ubuntu server security hardening guide provides a solid foundation for protecting your infrastructure. Implement these measures systematically, testing each change in a non-production environment first. With proper Ubuntu server security hardening, your servers will be well-defended against the majority of automated and targeted attacks.
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.