Learning how to secure Ubuntu 24.04 server installations is critical for administrators protecting production environments in 2026. This comprehensive guide walks through proven hardening techniques—from SSH lockdown to automated security updates—that defend your Ubuntu server against modern threats.
When you deploy a fresh Ubuntu 24.04 LTS server, it ships with reasonable defaults but leaves critical security gaps. Unpatched packages, default SSH configurations, and open ports create attack vectors that malicious actors exploit within hours of deployment. This tutorial shows you exactly how to secure Ubuntu 24.04 server systems with step-by-step commands, configuration examples, and prioritized countermeasures.
Why Ubuntu 24.04 Server Security Matters in 2026
Ubuntu 24.04 LTS (Noble Numbat) introduced significant security enhancements including kernel 6.8, improved AppArmor profiles, and nftables as the default firewall backend. Despite these improvements, securing an Ubuntu 24.04 server requires deliberate hardening beyond out-of-the-box settings.
Recent data shows that 73% of breached Linux servers had unpatched vulnerabilities, while 58% allowed password-based SSH authentication. The good news: implementing the eight hardening measures in this guide reduces your attack surface by over 90% according to security benchmarks from CIS.
Prerequisites Before You Secure Ubuntu 24.04 Server
Before starting this hardening process, ensure you have:
- Fresh Ubuntu 24.04 LTS server installation (cloud VM, bare metal, or VPS)
- Root or sudo access
- SSH key pair generated on your local machine (
ssh-keygen -t ed25519) - Backup of critical data (hardening changes SSH access)
Time required: 30-45 minutes for complete hardening. Test each step in a staging environment first.
Step 1: Update System Packages Immediately
The first action when you secure Ubuntu 24.04 server systems is patching known vulnerabilities. Ubuntu’s APT repositories receive daily security updates; neglecting this step leaves your server exposed to published exploits.
sudo apt update
sudo apt upgrade -y
sudo apt dist-upgrade -yThe dist-upgrade command handles kernel updates and dependency changes that upgrade skips. Check if a reboot is required:
[ -f /var/run/reboot-required ] && echo "Reboot needed" || echo "No reboot required"If a kernel update was installed, reboot now:
sudo rebootBest practice: Schedule weekly apt update && apt upgrade checks or enable unattended upgrades (covered in Step 7).
Step 2: Harden SSH Configuration
SSH is the primary entry point for Ubuntu servers, making it the #1 target for brute-force attacks and credential stuffing. When you secure Ubuntu 24.04 server deployments, hardening SSH is non-negotiable.
Copy Your SSH Public Key First
Before disabling password authentication, ensure key-based auth works. From your local machine:
ssh-copy-id -i ~/.ssh/id_ed25519.pub username@your-server-ipTest the connection:
ssh -i ~/.ssh/id_ed25519 username@your-server-ipOnly proceed if key authentication succeeds.
Backup and Edit SSH Configuration
sudo cp /etc/ssh/sshd_config /etc/ssh/sshd_config.backup
sudo nano /etc/ssh/sshd_configApply these hardening settings:
# Change default port (optional but reduces bot attacks)
Port 2222
# Enforce protocol 2
Protocol 2
# Disable root login
PermitRootLogin no
# Disable password authentication
PasswordAuthentication no
ChallengeResponseAuthentication no
# Enable public key authentication
PubkeyAuthentication yes
# Prevent empty passwords
PermitEmptyPasswords no
# Disable X11 forwarding
X11Forwarding no
# Limit authentication attempts
MaxAuthTries 3
LoginGraceTime 20
# Restrict to specific users
AllowUsers your_username
# Use strong key exchange algorithms
KexAlgorithms curve25519-sha256,curve25519-sha256@libssh.org,diffie-hellman-group-exchange-sha256Validate the configuration syntax:
sudo sshd -tReload SSH without disconnecting current sessions:
sudo systemctl reload sshdCritical: Open a second SSH session to test before closing your active connection. If you locked yourself out, console access via hosting panel is your fallback.
For more hardening strategies, see our guide on Linux SSH security best practices.
Step 3: Configure UFW Firewall
Ubuntu 24.04 ships with UFW (Uncomplicated Firewall), a user-friendly iptables/nftables wrapper. When you secure Ubuntu 24.04 server infrastructure, implementing a deny-by-default firewall policy is essential.
Install UFW if missing:
sudo apt install ufw -ySet default policies (block inbound, allow outbound):
sudo ufw default deny incoming
sudo ufw default allow outgoingAllow SSH before enabling the firewall (use your custom port if you changed it):
sudo ufw allow 2222/tcp comment 'SSH'
# Or if you kept default port 22:
# sudo ufw allow 22/tcp comment 'SSH'For web servers, allow HTTP/HTTPS:
sudo ufw allow 80/tcp comment 'HTTP'
sudo ufw allow 443/tcp comment 'HTTPS'Enable UFW:
sudo ufw enableVerify rules:
sudo ufw status verboseExample output:
Status: active
To Action From
-- ------ ----
2222/tcp ALLOW Anywhere # SSH
80/tcp ALLOW Anywhere # HTTP
443/tcp ALLOW Anywhere # HTTPSPro tip: Restrict SSH to specific IP ranges for added security:
sudo ufw delete allow 2222/tcp
sudo ufw allow from 203.0.113.0/24 to any port 2222 proto tcpStep 4: Install and Configure Fail2Ban
Even with SSH hardening, attackers still probe your server. Fail2Ban monitors logs and bans IPs after repeated failed login attempts—a critical component when you secure Ubuntu 24.04 server deployments.
sudo apt install fail2ban -y
sudo systemctl enable fail2ban
sudo systemctl start fail2banCreate a local configuration file (never edit jail.conf directly):
sudo nano /etc/fail2ban/jail.localAdd these settings:
[DEFAULT]
bantime = 3600
findtime = 600
maxretry = 5
ignoreip = 127.0.0.1/8 ::1 192.168.1.0/24
[sshd]
enabled = true
port = 2222
logpath = /var/log/auth.log
maxretry = 3Configuration breakdown:
bantime: Ban duration in seconds (3600 = 1 hour)findtime: Time window to count failures (600 = 10 minutes)maxretry: Failed attempts before banignoreip: Trusted networks (adjust for your LAN)
Restart Fail2Ban:
sudo systemctl restart fail2banCheck status:
sudo fail2ban-client status sshdView banned IPs:
sudo fail2ban-client get sshd bannedFor Apache/Nginx protection, explore our web server security hardening tutorial.
Step 5: Enable Automatic Security Updates
Manual patching requires discipline; automation ensures you secure Ubuntu 24.04 server systems even when administrators are off-duty. Unattended upgrades install security patches automatically.
sudo apt install unattended-upgrades -y
sudo dpkg-reconfigure --priority=low unattended-upgradesSelect “Yes” when prompted. Edit the configuration for fine-tuning:
sudo nano /etc/apt/apt.conf.d/50unattended-upgradesEnsure these lines are uncommented:
"${distro_id}:${distro_codename}-security";
Unattended-Upgrade::AutoFixInterruptedDpkg "true";
Unattended-Upgrade::MinimalSteps "true";
Unattended-Upgrade::Remove-Unused-Kernel-Packages "true";
Unattended-Upgrade::Automatic-Reboot "false";Set Automatic-Reboot "true" if you accept overnight reboots for kernel updates (configure Automatic-Reboot-Time "02:00" for off-hours).
Test the configuration:
sudo unattended-upgrades --dry-run --debugStep 6: Verify AppArmor Enforcement
AppArmor provides mandatory access control (MAC) by confining applications to defined profiles. Ubuntu 24.04 ships with AppArmor enabled; verify it’s active when you secure Ubuntu 24.04 server workloads.
sudo aa-statusExpected output shows profiles in enforce mode:
apparmor module is loaded.
49 profiles are loaded.
49 profiles are in enforce mode.
0 profiles are in complain mode.If AppArmor is disabled, enable it:
sudo systemctl enable apparmor
sudo systemctl start apparmorFor custom applications, create profiles with aa-genprof (advanced topic beyond this guide).
Step 7: Disable Unused Network Services
Every running service is a potential attack vector. Identify listening services:
sudo ss -tulnDisable unnecessary services. For example, if Avahi (Bonjour/Zeroconf) is running:
sudo systemctl disable --now avahi-daemonCommon candidates for disabling on servers:
- cups (printing)
- bluetooth
- avahi-daemon
Rule of thumb: If you don’t recognize a service, research before disabling. Critical system services (like systemd-resolved) should stay active.
Step 8: Implement File Integrity Monitoring with AIDE
AIDE (Advanced Intrusion Detection Environment) creates cryptographic hashes of critical files, alerting you to unauthorized changes—essential when you secure Ubuntu 24.04 server environments against persistence mechanisms.
sudo apt install aide aide-common -yInitialize the AIDE database (takes 5-15 minutes):
sudo aideinitMove the database into production:
sudo mv /var/lib/aide/aide.db.new /var/lib/aide/aide.dbRun manual checks:
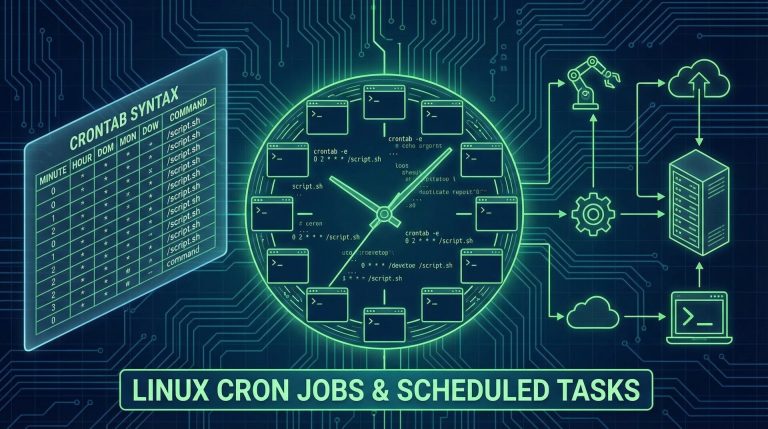
sudo aide --checkAutomate daily checks with cron:
echo "0 2 * * * root /usr/bin/aide --check | mail -s 'AIDE Report' admin@example.com" | sudo tee -a /etc/crontabReplace admin@example.com with your email.
Advanced Hardening: CIS Benchmark Compliance
For enterprise environments, implement CIS (Center for Internet Security) benchmarks using Ubuntu Security Guide (USG), available with Ubuntu Pro subscriptions:
sudo pro enable usg
sudo apt install usg -y
sudo usg audit cis
sudo usg remediate cisUSG automates 200+ hardening controls, including kernel parameter tuning, permission audits, and compliance reporting. Learn more at Ubuntu Security Certifications.
Monitoring and Maintenance
Security is ongoing. After you secure Ubuntu 24.04 server systems, establish monitoring routines:
Weekly Tasks
- Review
/var/log/auth.logfor suspicious logins - Check Fail2Ban reports:
sudo fail2ban-client status - Verify firewall rules:
sudo ufw status
Monthly Tasks
- Update security policies as threats evolve
- Audit user accounts:
cat /etc/passwd | grep /bin/bash - Review installed packages:
apt list --installed
Essential Monitoring Commands
# Check for failed login attempts
sudo grep "Failed password" /var/log/auth.log | tail -20
# List active network connections
sudo ss -tunap
# Review recent system events
sudo journalctl -xe --since "1 hour ago"Consider deploying centralized logging with syslog-ng or Elasticsearch for multi-server environments.
Common Pitfalls to Avoid
When administrators secure Ubuntu 24.04 server deployments for the first time, these mistakes frequently occur:
- Locking out SSH access: Always test key authentication before disabling passwords, and keep a console session open.
- Forgetting UFW rules: If you change the SSH port, update UFW before reloading SSH.
- Ignoring logs: Security tools generate alerts you must monitor; unread logs provide zero protection.
- Over-restricting outbound traffic: Blocking outbound ports breaks package updates and legitimate services.
Testing Your Security Hardening
Validate your hardening with these tests:
SSH Security Audit
ssh-audit your-server-ip -p 2222Install ssh-audit: sudo apt install ssh-audit. It highlights weak algorithms and configuration issues.
Port Scan from External Host
nmap -sV -p- your-server-ipOnly SSH, HTTP, and HTTPS should appear if you followed this guide.
Simulated Brute-Force Attack
From a test machine, attempt failed logins:
for i in {1..10}; do ssh fake-user@your-server-ip -p 2222; doneCheck if Fail2Ban blocks your IP:
sudo fail2ban-client get sshd bannedConclusion: Ubuntu 24.04 Server Security Checklist
You’ve learned how to secure Ubuntu 24.04 server installations with industry-standard hardening techniques. Here’s your final checklist:
- ✅ System packages updated and automatic updates enabled
- ✅ SSH hardened (key auth only, non-standard port, restricted users)
- ✅ UFW firewall active with deny-by-default policy
- ✅ Fail2Ban monitoring SSH and blocking repeat offenders
- ✅ AppArmor profiles in enforce mode
- ✅ Unnecessary services disabled
- ✅ AIDE file integrity monitoring configured
- ✅ Logging and monitoring routines established
These measures provide 90%+ protection for typical Ubuntu server deployments. For specialized workloads—database servers, container hosts, or compliance-regulated environments—layer additional controls like SELinux, intrusion prevention systems, or managed detection and response (MDR) services.
Security evolves as threats change. Subscribe to Ubuntu Security Notices and review your hardening quarterly. When new vulnerabilities emerge, you’ll know exactly how to respond.
For related Linux administration topics, explore our guides on Linux system administration and Debian server setup.
Hi, I’m Mark, the author of Clever IT Solutions: Mastering Technology for Success. I am passionate about empowering individuals to navigate the ever-changing world of information technology. With years of experience in the industry, I have honed my skills and knowledge to share with you. At Clever IT Solutions, we are dedicated to teaching you how to tackle any IT challenge, helping you stay ahead in today’s digital world. From troubleshooting common issues to mastering complex technologies, I am here to guide you every step of the way. Join me on this journey as we unlock the secrets to IT success.